Cloud Computing and Data Security go Hand in Hand
Cloud computing has become a loosely used buzzword in recent years. The term is so commonly used, that even if you are a non-IT person, you are expected to know something about it. As per Gartner’s IT Glossary, it is “a style of computing in which scalable and elastic IT-enabled capabilities are delivered as a service using Internet technologies.” This includes both software and hardware. In simple terms, it means that your data, applications, and even your hardware could be hosted by a service provider on multiple (or dedicated) servers. This model of cloud computing services is true distributed computing in real terms.

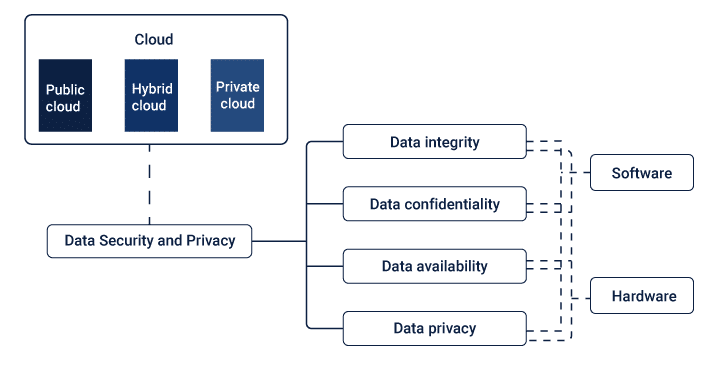
The Data Security Landscape

While the shift to cloud computing services has been happening for a while, the security concerns surrounding data is still a much-discussed subject. Does cloud computing provide data privacy and security? Or is it prone to breaches? What kind of countermeasures are being employed by the service provider so that the sanctity of the data is maintained at all times? There are many who believe that a company has more control over its data when it is housed in its own premises, or at best, kept in a private cloud. However, many others beg to differ.
They feel that the cloud computing services provider is specialized, has better systems, employs more trained personnel, possesses a 360-degree view of both the data and infrastructure and can be on constant alert to any security compromises. Let us examine the type of data security concerns in cloud computing services environment. This will also tell us about the data security measures that are being deployed to overcome them. This is an evolving landscape and the list of security measures is growing endlessly to combat different types of cyber-attacks, viruses, breaches, leakages, accidental loss, theft, etc. We will only discuss a few of the critical ones.
Data Privacy and Privacy Protection
In today’s world, no subject is getting more attention in the media than the privacy and protection of one’s data. Customer data, electoral data, and financial data are compromised every day, and there are many laws and regulations in place to safeguard this data. Even if the loss happens because of the service provider, the company that owns the data or takes responsibility for processing the data is liable. So, the cloud services provider has to demonstrate to his client that the measures that they have in place are almost fail-proof. There are many forms of contracts that can be entered into with the cloud computing services provider, with proper SLAs (Service Level Agreement) to exactly define the areas of responsibility for both the parties.
Data Integrity
In computing Data Integrity is vital. Any tampering, modification, or deletion of data can be very dangerous and costly. In a cloud computing services environment data can be easily lost or contaminated because of being accessed by unauthorized personnel or a systems breach. Better authentication and authorization protocols are needed to main the sanctity of the data. Two-factor authentication is one such protocol.
Data Availability
Data can be of various types. They can be structured or unstructured, in-transit or at-rest, or rarely used (as in back-up or disaster recovery data). Different service providers recognize this aspect of data and have tuned their cloud storage services to address this. The response time of data or its availability at the exact required moment is vital.
Cloud computing, which shares its storage environments among multiple clients, can sometimes create a situation where there is latency when retrieving the data of a particular client. But for critical processes, data may need to be stored in specified regions where they can be accessed quickly. This is a capability that the cloud computing services provider needs to build into its cloud infrastructure.
Encryption
Today no data is sent across the internet or any open network without being encrypted. It is one of the mainstays of data privacy and offers the best protection against external threats. A plethora of Machine Learning algorithms and techniques are used to encrypt data to keep it from being compromised. But different types of data require different encryption and decryption techniques, and all such procedures need to be specifically requested from the service provider. It also needs to be spelled out clearly in the SLA.
Security Lapses by Authorised Personnel
Data can be compromised by employees, contractors, and other stakeholders due to carelessness or human error. Of course, it can also be done on purpose by malicious or disgruntled staff members. The staff members who have access to data, especially critical data, need to be trained and constantly made aware of the threat they pose to the organization’s data. Perhaps, more security lapses happen because of employee carelessness than any other major external threat.
Threats
All threats are not necessarily data related. They can be because of infrastructural factors also: from compromised networks to sharing of host machines, from inelegance of the Virtual Machine (VM) to employee carelessness.
- Simple Breaches: There are many types of threats that originate from hacked accounts, lost passwords, open applications, or even virtual machine errors. Such breaches can be prevented through constant supervision and quick action is necessary to redress any problem. Regular backing-up of data, constant checks, and changing of access codes, etc. can prevent major calamities.
- Hijacked accounts, or even APIs, can cause much damage to the data in the cloud environment – it can be compromised very quickly without alerting any normal detection system.
- DoS Attacks: Denial of Service is a very common threat. If this happens, clients may not be able to access applications or data and can cause panic. Depending on the application or interface, a wrong message to a client showing Denial of Service can lead to embarrassment or even non-renewal of contracts in the long run. A system has to be up at all times for the client to feel confident about the service he/she is paying for.
- Malware Injections: These are scripts that run as valid SaaS programs inside the cloud. They can be used for contaminating data or disrupting performance, or worse.
- Network Security: The network is the most common doorway through which threats can enter. The data needs to be secure at all times, especially since it is traveling over the internet. Strong network traffic encryption techniques need to be put in place by the service provider to ensure less vulnerability on this front.
Summary
Here, we looked at the cloud computing services environment and the benefits it provides to clients. However, the data security landscape is vulnerable and prone to data compromises from internal or external sources. We have then looked at the challenges posed to data in its various forms and some of the solutions that both the cloud service provider and the client can contractually take responsibility for. We have also looked at the important cloud-specific threats, both internal and external, data related or environment related. In conclusion, all we can say is that cloud computing is here to stay. Though, the landscape of data security will always pose challenges that need to be constantly monitored, detected, and resolved.Must Reads:
[wcp-carousel id=”10006″]
